
🚀 The Future Is Here
Dive Into the Immersive Tech Revolution
Virtual Reality Visionary brings you cutting-edge insights, expert analyses, and comprehensive guides on VR technology, digital innovation, and the future of computing. Stay ahead of the curve with in-depth features covering everything from gaming headsets to enterprise applications.
Explore Our Tech Universe
Comprehensive coverage across all dimensions of digital innovation
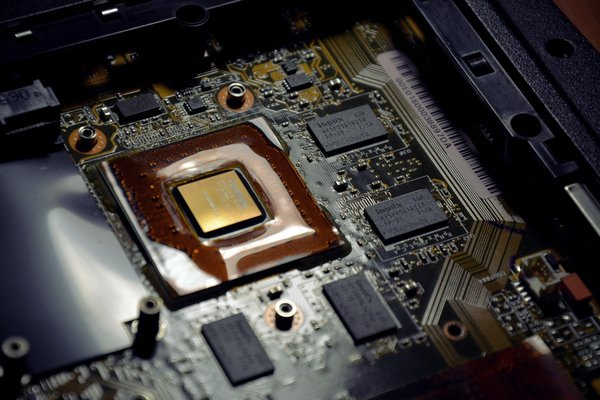
Hardware
Components, PCs and peripherals
View articles →High tech
Innovations and new technologies
View articles →Internet
Web, social media and online services
View articles →Marketing
Digital marketing and SEO
View articles →News
Tech and computing news
View articles →Smartphones
Phones, tablets and apps
View articles →Video games
Video games, consoles and gaming
View articles →“
This blog has become my go-to resource for understanding VR technology. The articles are thorough, well-researched, and always up-to-date with the latest developments. I've learned more here than anywhere else.
Latest articles
Our recent publications


Hardware
Essential Tips for Building a Secure Home Office Network with the Linksys MX5 Velop AX WiFi 6 System
Hardware
How do you optimize a Lenovo ThinkPad X1 Carbon for remote work with multiple external monitors?

Hardware
How to install and configure a two-factor authentication system on a Windows 10 machine using YubiKey?

Hardware
What are the best practices for setting up a secure and efficient home automation system using a Google Nest Hub?

Hardware
What are the steps to set up a virtualized environment on a HP ProLiant DL380 Gen10 for running multiple isolated applications?

High tech
How can AI be leveraged to enhance the cybersecurity of critical infrastructure?

High tech
How can blockchain ensure the security of decentralized autonomous organizations (DAOs)?
High tech
How to develop an AI-driven platform for early disease detection in healthcare?

High tech
What are the key steps to implement a real-time fraud detection system using machine learning?

High tech
What are the steps to create an AI-driven financial forecasting model?

High tech
What are the techniques for optimizing AI-driven chatbots for multilingual support?

Internet
Essential Strategies for Effective Rate Limiting in Your RESTful API

Internet
How can you integrate Google Firebase for user authentication in a React application?

Internet
How can you use Azure Cognitive Services for natural language processing in a chatbot?

Internet
How do you set up cross-region replication for Amazon S3 to ensure data redundancy?

Internet
What are the best practices for implementing a secure GraphQL API in Node.js?

Internet
What are the steps to configure Kubernetes Helm charts for application management?

Marketing
Boosting Student Engagement: Innovative Data Analytics Strategies for UK Universities

Marketing
Crafting an Eco-Friendly Digital Marketing Blueprint for the UK Food and Beverage Sector: Essential Steps to Success

Marketing
Essential Steps for Crafting a Responsive Design for UK Government Websites

Marketing
Essential Steps to Develop a Safe Blockchain Voting System for Local Elections in the UK

Marketing
Essential Strategies for UK Ecommerce Platforms to Enhance Cross-Border Transaction Efficiency

Marketing
How to optimize UK-based travel websites for voice search?

News
Discover the Cutting-Edge AI Breakthroughs Revolutionizing Agriculture in the UK

News
Essential Elements of an Effective Cybersecurity Framework for UK Schools and Universities

News
Essential Factors to Consider When Integrating AI into Public Libraries Across the UK

News
Exploring Cutting-Edge AI Innovations Transforming Renewable Energy in the UK
News
Exploring the Latest Trends in AI-Powered Content Creation for the UK Media Landscape

News
How Are UK Retailers Utilizing AI to Enhance Loyalty Programs?
Frequently Asked Questions
What topics does Virtual Reality Visionary cover?
We cover a wide range of computing and tech topics including VR hardware, gaming technology, smartphones, internet trends, marketing innovations, and general high-tech news. Our focus is on immersive technologies and how they're shaping the digital landscape.
How often is new content published?
We publish fresh articles daily, with major features and in-depth analyses released several times per week. Our team of contributors ensures a steady stream of high-quality content across all our categories. Breaking news and urgent updates are posted as events unfold.
Are the reviews and analyses biased?
All our content is independently researched and written without external influence. We maintain strict editorial standards and do not accept compensation for coverage or reviews. Our contributors disclose any potential conflicts of interest, ensuring you receive honest, unbiased information.
Can I contribute articles to the site?
We welcome contributions from experienced tech writers and industry professionals. If you have expertise in VR, computing, or related fields and would like to share your insights, you can reach out through our contact page with your writing samples and proposed topics for consideration.
